So one of the requests I get fairly regularly when working with SCOM is can SCOM alert when users are added to the Domain Administrators group. The answer is YES, and as it turns out this is quite an easy thing to accomplish. It is very similar to the blog I wrote a while back on How to Generate Alerts from Event Logs. The major difference is we will be doing this with a Rule, not a Monitor.
Build the Custom Rule:
Open up the SCOM console and go to Authoring > Management Pack Objects > Rules. In the Tasks window Click Create a Rule
When the Create Rule Wizard runs, drill down to Alert Generating Rules > Event Based and Select NT Event Log (Alert). Select a custom management pack, or create one if you don't have one yet. Click Next
Give it a unique name similar to below. I worded it this way as I will also setup a rule to monitor when users are removed from this group (discussed later in this segment). Add a clear description as well. Rule Category is Alert and be sure to set Windows Domain Controller as the Rule target. Check Rule is enabled and Click Next.
For Event Log Name click the ... on the right. Be sure one of your domain controllers is in the Computer field. Then select the Security log. Click OK
Log name should read Security. If not repeat the previous step. Click Next
For Event ID you want 4728 and change Event Source to Parameter 3 and equals Domain Admins. Click Next
I modified the Alert Description a little bit to pass through additional information. I also changed the Priority to High. Click Create
Give it a bit of time to propagate throughout your environment and test it by adding someone to the DA group.
This process can be expanded to removing users from the Domain Admins group as well as adding / removing from Schema Admins and Enterprise Admins by using the information below:
Domain Admins
Security Group Alert - User Added to Domain Admins
Event ID = 4728
Parameter 3 = Domain Admins
Security Group Alert - User Removed from Domain Admins
Event ID = 4729
Parameter 3 = Domain Admins
Schema Admins
Security Group Alert - User Added to Schema Admins
Event ID = 4756
Parameter 3 = Schema Admins
Security Group Alert - User Removed from Schema Admins
Event ID = 4757
Parameter 3 = Schema Admins
Enterprise Admins
Security Group Alert - User Added to Enterprise Admins
Event ID = 4756
Parameter 3 = Enterprise Admins
Security Group Alert - User Removed from Enterprise Admins
Event ID = 4757
Parameter 3 = Enterprise Admins
In the next segment I will show you how to protect the security groups using SCORCH.
More to come!
If you like this blog, give it a g+1
Friday, June 17, 2016
Tuesday, June 7, 2016
SCCM 2012 - How to Deploy SCOM 2012 Agent
So now that we have SCCM 1511 up and running I wanted to setup up a deployment for the SCOM agent. This is actually a very simple application to setup.
Gather SCOM Agent Files:
So the first thing we need is the SCOM Agent files. On your SCOM server navigate to %ProgramFiles%\System Center 2012\Operations Manager\Server\AgentManagement. You will see AgentLogs, amd64, UnixAgents and x86. Since all the servers in my lab are 64bit I am going to copy the amd64 folder over to my app catalog on my SCCM server. I plan to cover multi-platform deployment in the next segment.
Create the Application:
Since this is an .msi we will be building an Application. On your SCCM server go to Software Library > Application Management > Applications. Right Click on Applications and choose Create Application. Type is .msi and you will need to browse to the share location of the MOMAgent.msi. Click Next
If you copied the entire amd 64 folder, all of your install files should be discovered successfully. Click Next
I like to be fairly detailed when building Applications. It makes it easier to manage them in the long run. Fill out the Application information as you feel is necessary. For Installation program you should fill it out as follows (updating the yellow text for your enveronment):
msiexec /i momagent.msi /qn USE_SETTINGS_FROM_AD=0 USE_MANUALLY_SPECIFIED_SETTINGS=1 MANAGEMENT_GROUP=Management Group Name MANAGEMENT_SERVER_DNS=FQDN of RMS Server ACTIONS_USE_COMPUTER_ACCOUNT=1 AcceptEndUserLicenseAgreement=1
Click Next
Review the summary and Click Next
Wait for it...
And Done!
One final step. Open the SCOM console and go to Administration > Settings > Security. Change the radio button to Review new manual agent installations in pending management view and Check Automatically approve new manually installed agents. This will allow all newly installed clients to be accepted into the Management Group without any administrator intervention.
Distribute the content and deploy to your servers collection and you are all set!
More to come!
If you like this blog, give it a g+1
Gather SCOM Agent Files:
So the first thing we need is the SCOM Agent files. On your SCOM server navigate to %ProgramFiles%\System Center 2012\Operations Manager\Server\AgentManagement. You will see AgentLogs, amd64, UnixAgents and x86. Since all the servers in my lab are 64bit I am going to copy the amd64 folder over to my app catalog on my SCCM server. I plan to cover multi-platform deployment in the next segment.
Create the Application:
Since this is an .msi we will be building an Application. On your SCCM server go to Software Library > Application Management > Applications. Right Click on Applications and choose Create Application. Type is .msi and you will need to browse to the share location of the MOMAgent.msi. Click Next
If you copied the entire amd 64 folder, all of your install files should be discovered successfully. Click Next
I like to be fairly detailed when building Applications. It makes it easier to manage them in the long run. Fill out the Application information as you feel is necessary. For Installation program you should fill it out as follows (updating the yellow text for your enveronment):
msiexec /i momagent.msi /qn USE_SETTINGS_FROM_AD=0 USE_MANUALLY_SPECIFIED_SETTINGS=1 MANAGEMENT_GROUP=Management Group Name MANAGEMENT_SERVER_DNS=FQDN of RMS Server ACTIONS_USE_COMPUTER_ACCOUNT=1 AcceptEndUserLicenseAgreement=1
Click Next
Review the summary and Click Next
Wait for it...
And Done!
One final step. Open the SCOM console and go to Administration > Settings > Security. Change the radio button to Review new manual agent installations in pending management view and Check Automatically approve new manually installed agents. This will allow all newly installed clients to be accepted into the Management Group without any administrator intervention.
Distribute the content and deploy to your servers collection and you are all set!
More to come!
If you like this blog, give it a g+1
Tuesday, May 31, 2016
SCCM 1602 - Update
So one of the really cool things they introduced with 1511 is Updates and Servicing. Remember in SCOM 1511 - Installation when we mentioned that you want to use the Configuration Manager cloud service?
This is part of that. It gives you the ability to do in place upgrades of SCCM as part of the SCCM "Current Branch". Minor version upgrades will come on a monthly basis, and Major upgrades will happen once every four months. Gone are the days of the service pack and update rollup. One think to note, all of the minor upgrades are included in the major update. So you can elect to skip the minors if you want and just install the majors. There were a few minor releases in 2015 but in November Microsoft released the first major, 1511. Get it? November of 2015. Microsoft actually did something that made sense. So in February of this year Microsoft released 1602 Below is a summary of the high points of the release. You can read the entire Technet article for additional information.
Whats New:

Check the features you want and Click Next
You can choose how you want to update the clients, either all or by testing on a specific collection. Click Next
Accept the EULA and Click Next
Review the summary and Click Next
Click Close and wait
There is a console upgrade in 1602 so as soon as the install finishes you will be prompted to update the console. Anyone who has a remote installation of the console will also be prompted.
When the console update finishes it will open back up again and you can track the progress of the client updates. You will notice that the Hierarchy Site Version
matches the Client version
Please keep in mind the size of your environment will dictate how long this process takes. Very large builds could take days or even weeks to update all of the clients.
Also, if you have not enabled automatic client updates Administration > Overview > Site Configuration > Sites > Hierarchy Settings > Client Upgrade Tab and check Upgrade all clients in the hierarchy using production client, the clients will not update on their own.
More to come!
If you like this blog, give it a g+1
This is part of that. It gives you the ability to do in place upgrades of SCCM as part of the SCCM "Current Branch". Minor version upgrades will come on a monthly basis, and Major upgrades will happen once every four months. Gone are the days of the service pack and update rollup. One think to note, all of the minor upgrades are included in the major update. So you can elect to skip the minors if you want and just install the majors. There were a few minor releases in 2015 but in November Microsoft released the first major, 1511. Get it? November of 2015. Microsoft actually did something that made sense. So in February of this year Microsoft released 1602 Below is a summary of the high points of the release. You can read the entire Technet article for additional information.
Whats New:
- Client Online Status: You can now view the online status of devices in Assets and Compliance. New icons indicate the status of a device as online or offline.
- Support for SQL Server AlwaysOn Availability Groups: Configuration Manager now supports using SQL Server AlwaysOn Availability Groups to host the site database.
- Windows 10 Device Health Attestation Reporting: You can now view the status of Windows 10 Device Health Attestation in the Configuration Manager console to ensure that the client computers have a trustworthy BIOS, TPM, and boot software.
- Office 365 Update Management: You can now natively manage Office 365 desktop client updates using the Configuration Manager Software Update Management (SUM) workflow. You can manage Office 365 desktop client updates just like you manage any other Microsoft Update.
- New Antimalware Policy Settings: New antimalware settings that can now be configured include protection against potentially unwanted applications, user control of automatic sample submission, and scanning of network drives during a full scan.
- Windows 10 Servicing: New improvements were added based on your feedback such as filters in servicing plans for upgrades that meet specified criteria, integration with deployment verification and a dialog in Software Center when starting an upgrade.
- Conditional Access for PCs Managed by Configuration Manager: You can now use conditional access capabilities to help secure access to Office 365 and other services on PCs managed with Configuration Manager agent. Conditions that can be used to control access include: Workplace Join, BitLocker, Antimalware, and Software Updates.
- Windows 10 Conditional Access Enhancements: For Windows 10 devices that are managed through the Intune MDM channel, you can now set and deploy an updated Compliance Policy that includes additional compliance checks and integration with Health Attestation Service.
- Microsoft Edge Configuration Settings: You can now set and deploy Microsoft Edge settings on Windows 10 devices.
- Windows 10 Team Support: You can now set and deploy Windows 10 Team configuration settings.
- Apple Volume Purchase Program (VPP) Support: You can now manage and deploy applications purchased through the Apple Volume Purchase Program for Business portal.
- iOS App Configuration: You can now create and deploy iOS app configuration policies to dynamically change settings such as server name or port for iOS applications that support these configurations.
- iOS Activation Lock Management: New capabilities include enabling iOS Activation Lock management, querying for the status, retrieving bypass codes, and performing an Activation Lock bypass on corporate-owned iOS devices.
- Kiosk Mode for Samsung KNOX Devices: Kiosk mode allows you to lock a managed mobile device to only allow certain apps and features.
- User Acceptance of Terms and Conditions: You can now see which users have or have not accepted the deployed terms and conditions.
How to install 1602:
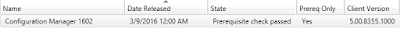
In Administration > Overview > Cloud Services > Updates and Servicing you should see this:

Note - If the update seems to be stuck in the "downloading" state for an extended period, restart the smsexec service to get it to finish.
Now that we have it downloaded we want to Right Click and select Run prerequisite check.
While the prerequisite checker is running you will see the state change to checking prerequisites. Once it is finished you will see prerequiste check passed.
Check the features you want and Click Next
You can choose how you want to update the clients, either all or by testing on a specific collection. Click Next
Accept the EULA and Click Next
Review the summary and Click Next
Click Close and wait
There is a console upgrade in 1602 so as soon as the install finishes you will be prompted to update the console. Anyone who has a remote installation of the console will also be prompted.
When the console update finishes it will open back up again and you can track the progress of the client updates. You will notice that the Hierarchy Site Version
matches the Client version
Please keep in mind the size of your environment will dictate how long this process takes. Very large builds could take days or even weeks to update all of the clients.
Also, if you have not enabled automatic client updates Administration > Overview > Site Configuration > Sites > Hierarchy Settings > Client Upgrade Tab and check Upgrade all clients in the hierarchy using production client, the clients will not update on their own.
More to come!
If you like this blog, give it a g+1
Thursday, May 26, 2016
SCCM 1511 - Installation
So a few years ago I did three segments on how to install SCCM 2012. It covered the WSUS installation and configuration, the SCCM prerequisite installs and the actual SCCM install. Since the time of those writings that method has become obsolete. A man by the name of Nickolaj Andersen wrote a very cool PowerShell based tool called the ConfigMgr Prerequisites Tool to run through all the pre-installation steps required. At the time of this writing it was on version 1.4.2 which supports SCCM 2012, SCCM 2012 R2 and SCCM Current Branch (1511+). So I am going to run through the updated 1511 install using this tool.
What you need before you begin:
When you first run the tool it does a validation check to see if reboots are required, you are on a supported server, you have a supported version of PowerShell and the account you are using is a local administrator on this machine. You will also notice the current supported SCCM versions in the lower left.
Then you will also be prompted for the \SMSSETUP\BIN\X64 folder so it can verify version information for the download
A lot better than doing it the hard way!
Since we have already downloaded the install files Select Use previously downloaded files and browse to the download location. Click Next
What you need before you begin:
- Download the tool (linked above)
- On your SCCM server set your PowerShell execution policy to Unrestricted.
- Set-ExecutionPolicy Unrestricted
- In Active Directory identify the Schema Master server
- In Active Directory create a service account called SCCMAdmin. This needs to be a SysAdmin on your SQL server and a Local Admin on all SCCM servers
- In Active Directory create a security group called SCCM Site Servers and add all the SCCM servers and the SCCM Admin account to this group
When you first run the tool it does a validation check to see if reboots are required, you are on a supported server, you have a supported version of PowerShell and the account you are using is a local administrator on this machine. You will also notice the current supported SCCM versions in the lower left.
Since we have Green Check marks across the board, lets begin!
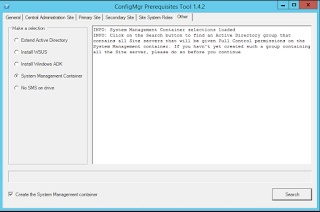
System Management Container:
If you click on the Other tab at the top and Select System Management Container. Check the box Create the System Management container and select Search.
Enter in the name of the security group created above and Click Search. Once it is found select it in the window below and Click OK. If you are not a member of Domain Admins you will not be able to add the selected group when you search.
This will go out to ADSI, create the Systems Management Container. It will then go to AD and add the security group defined above and set delegation permissions for it.
Extend Active Directory Schema:
Now click on the Extend Active Directory Schema radio button. You will be asked for the name of the Schema Master server name. Once you enter it in Click Extend. If you are not a member of Schema Admins you will get an error at this point.
You will be prompted for the location of the SMSSETUP\BIN\X64 folder so it can locate the extadsch.exe file to execute the AD Schema extension.
Verify that it was successful
Windows ADK:
Next we will install the Windows Assessment and Deployment Kit. Select the Install Windows ADK radio button. You will see that you have two installation Methods available to you, Offline and Online. If you have already downloaded the ADK you can do an offline install, otherwise select Online. You can also install either ADK 8.1 or ADK 10. Since we are going to install SCCM 1511, ADK 10 is required. Click Install
Verify it was successful
Install WSUS:
Now select the Install WSUS radio button. Since I already have SQL 2014 SP1 installed I am going to leverage that for the WSUS install. You can also use the Windows Internal Database if you choose. After filling in the appropriate information Click Install
You will be prompted for a save location for the WSUS Content. I created a new folder on c:\ called WSUS Content and Clicked OK
Note - This is obviously not an ideal configuration. In a production environment you would not want this on the c:\ but since this is just a lab it didn't matter
All good!
Note - Since we are also going to be supporting Windows 10 in this lab you will need to download and install KB3095113 which provides WSUS support for Windows 10 feature upgrades.
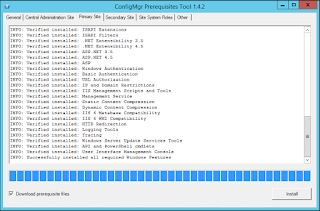
Primary Site Prerequisite Installs:
We are going to be building a Primary site so Click on the Primary Site Tab. Be sure to Check the box Download prerequisite files and Click Install
You will be prompted for a save location for the downloads after all the roles and features are installed. I created a new folder c:\downloads
Then you will also be prompted for the \SMSSETUP\BIN\X64 folder so it can verify version information for the download
A lot better than doing it the hard way!
SCCM Install:
Now that the server is prepped (and in record time), we are ready to run the SCCM install. If you are not logged in as the SCCMAdmin account do so now. Double Click on splash.hta. Make sure you have Version 1511. Click Install
Click Next
Select Install a Configuration Manager primary site and Click Next
Click Next
Select Install a Configuration Manager primary site and Click Next
Enter your license key and Click Next
Accept the EULA and Click Next
I am still surprised this has not been changed. Accept all three (even though we wont be using SQL Server Express). Click Next
The install will verify that all files needed are present
Select all appropriate server languages and Click Next
Select all appropriate client languages and Click Next
Enter a site code and site name. You can also modify the install location. Click Next
This is going to be a new stand alone primary so select Install the primary site as a stand-alone site and Click Next
Nice feature added in 2012 R2. You can add additional members of the hierarchy at a later time if you need to. Select Yes
Verify your SQL installation information and Click Next
You can modify the file locations if your SQL procedures dictate. Click Next
Since we only have the one Primary, Click Next
Choose Configure the communication method on each site system role and Click Next
We want this server to be a Management Point and a Distribution Point so Click Next
Click Next
This is a great new feature which I will cover in a subsequent segment. Select Yes, let's get connected and Click Next
Review your install summary and Click Next
I had to change the SQL Server Service to Network Service or Local System to resolve the failure. Click Run Check
These warnings can be ignored. Click Begin Install
Eighteen minutes later (more or less) and we are all done! Click Close and Exit from the installer
From here you can open the console and begin using SCCM 1511!
More to come!
If you like this blog, give it a g+1
Subscribe to:
Comments (Atom)